Relational Database
Flipt supports the following relational databases: SQLite is enabled by default for simplicity, however, you should use PostgreSQL, MySQL, or CockroachDB if you intend to run multiple copies of Flipt in a high availability configuration. The database connection can be configured as follows:SQLite
The default location of the SQLite database is
/var/opt/flipt/flipt.db on
Linux and ~/Library/Application Support/flipt/flipt.db on macOS.- Environment Variables
- Configuration YAML
LibSQL
See our libSQL Example for a working example of how to use libSQL with Flipt.Local
- Environment Variables
- Configuration YAML
Remote
If using Turso you must use a database auth
token
to access the database.
- Environment Variables
- Configuration YAML
PostgreSQL
- Environment Variables
- Configuration YAML
CockroachDB
- Environment Variables
- Configuration YAML
MySQL
- Environment Variables
- Configuration YAML
Migrations
From time to time the Flipt database must be updated with new schema. To accomplish this, Flipt includes amigrate command that will run any pending
database migrations for you.
By default Flipt will run your application data migrations. You can run migrations on your analytical databases by specifying the --database=analytics flag to the migrate command.
If Flipt is started and there are pending migrations, you will see the following
error in the console:
$HOME/flipt is just used as an example, you can use any directory you would
like on the host.Declarative
The following backend types are designed to support declarative management of feature flag state via a well-known file format. In particular, they’re designed to support GitOps practices with minimal external dependencies. The current four declarative backend types include:The
local backend has been primarily developed to support a local
development experience, whereas, the git, object and oci backends are
intended for production use.Read Only Mode
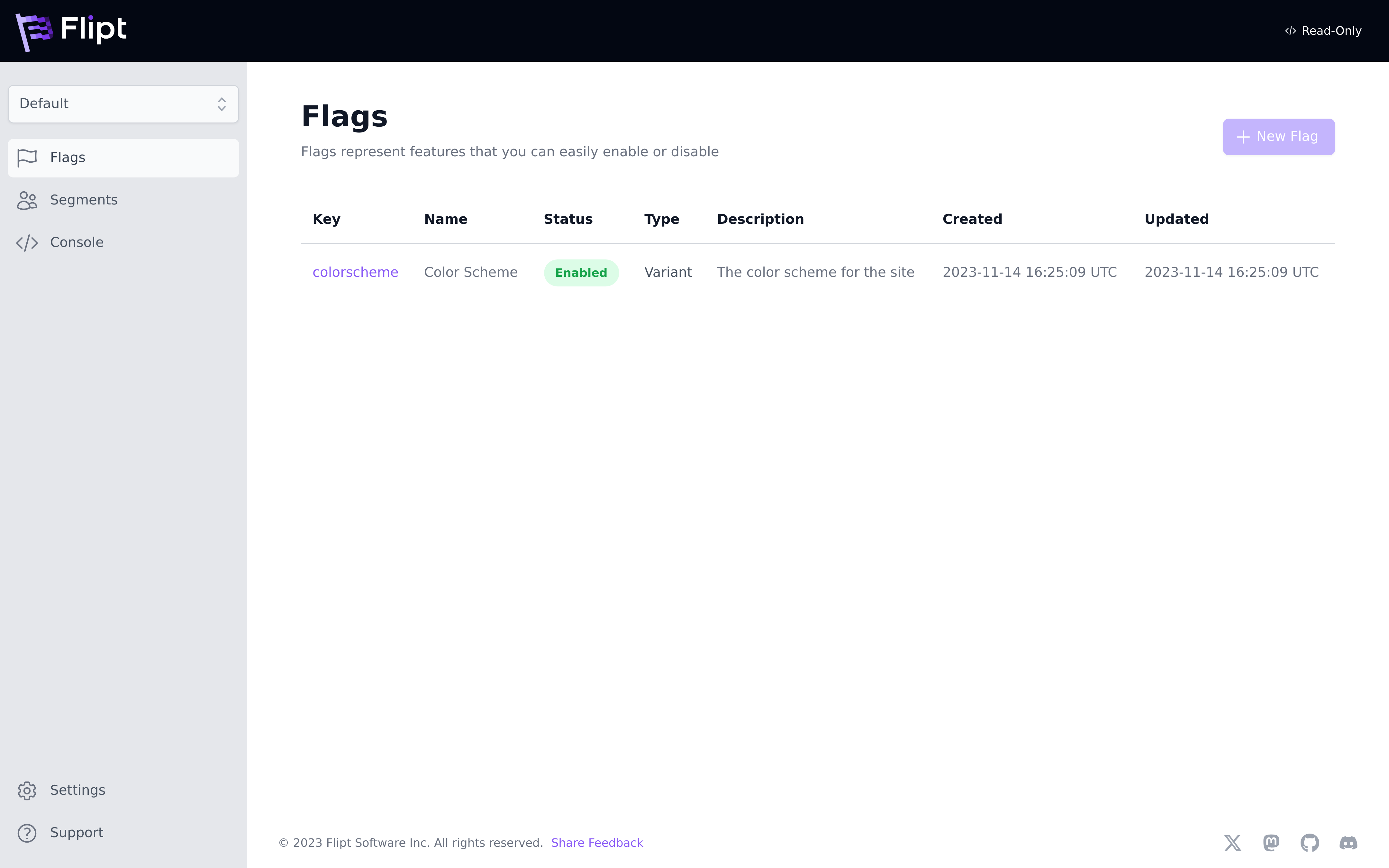
read-only mode that prevents Flipt from writing to the backend. This is useful for production environments where you want to ensure that flag state is only managed via the configured backend.
Local
The purpose of this backend type is to support serving Flipt flag state directly from your local filesystem. You can simply specify a relative or absolute directory in order to start a local Flipt instance and serve flag state. This is particularly useful for local development and validation of flag state changes. Flipt will periodically rebuild its state from the local disk every 10 seconds.- Environment Variables
- Configuration YAML
Git
Thegit type backend is used to configure a target Git repository and Git reference to source feature flag state.
The configuration contains fields for addressing the repository, configuring the target reference as well as adding authentication credentials.
Once a target repository and reference are configured, Flipt will poll the source repository on a periodic cadence.
This cadence is also configurable and defaults to 30 seconds.
Flipt will follow the configured reference and keep up to date with new changes.
Flipt supports the following reference types:
static(default): Flipt will use the reference provided in the configuration.semver: Flipt will use the latest reference that matches the semver pattern (e.g.v1.0.*).
- Environment Variables
- Configuration YAML
Authentication
Authentication enables the ability to leverage private Git repositories as flag state backends. Thegit type backend supports both basic, token and ssh based authentication schemes.
GitHub
When using GitHub and their PATs (Personal Access
Tokens),
basic authentication should be used. GitHub expects you to supply a valid
username and provide your PAT as the password parameter.storage.git.authentication.ssh configuration section:
Repository Storage
Thegit backend also supports configuring where the Git repository is cloned to.
By default, Flipt will clone the repository to an in-memory filesystem, but you can configure a local directory to clone the repository to which is useful for relieving memory pressure especially for large repositories.
Object
The object storage type supports using a hosted object storage service as the source of truth for Flipt state configuration. Currently, Flipt supports the following object store providers:Contents
The contents of a target object storage bucket must contain Flipt state configuration files. As with thegit and local backend types, the same rules apply with regard to how Flipt will locate feature flag state in your target bucket.
See the section below on Flag State Configuration for how Flipt decides which files in a target are considered for serving flag state.
With the object storage backend, Flipt will respect a file at the root of the target with the name .flipt.yml to serve as an index for locating flag state configuration in the bucket.
It will also use the same default strategy when the index isn’t supplied (e.g. file name features.yml or *.features.yml).
Amazon S3
The AWS S3 backend can be configured to serve state from a single bucket from a target S3-compatible API. This means that both AWS S3 and open-source alternatives such as Minio can be used. The following is an example of how to configure Flipt to leverage this backend type:- Environment Variables
- Configuration YAML
In addition to these Flipt configuration parameters, valid credentials will
also be required for Flipt to authenticate with the target object store.
Azure Blob Storage
The Azure Blob Storage backend can be configured to serve state from a single container from a target Azure Blob Storage account. The following is an example of how to configure Flipt to leverage this backend type:- Environment Variables
- Configuration YAML
In addition to these Flipt configuration parameters, valid credentials will
also be required for Flipt to authenticate with the target object store.
- Using Azure Credentials
- Using Azure Blob Storage Account Keys
Google Cloud Storage
The Google Cloud Storage backend can be configured to serve state from a single bucket from a target Google Cloud Storage account. The following is an example of how to configure Flipt to leverage this backend type:- Environment Variables
- Configuration YAML
In addition to these Flipt configuration parameters, valid credentials will
also be required for Flipt to authenticate with the target object store.
OCI
Sincev1.31.0, Flipt supports using any OCI compatible registry as a declarative backend source.
Flipt has its own custom OCI manifest format (we call them bundles), which can be built and managed using the Flipt CLI.
- Environment Variables
- Configuration YAML
Certain OCI registries may require setting the OCI manifest version to something other than the default (
1.1) to work correctly.In this case, you can set the FLIPT_STORAGE_OCI_MANIFEST_VERSION environment variable or storage.oci.manifest_version configuration property to the desired version (e.g. 1.0).See this issue for more information.Authentication
Starting from version1.40.0, Flipt offers two authentication methods:
- Static: This is the default method that uses a username and password for authentication.
- AWS ECR: If you’re using Flipt on AWS with a private ECR repository, you can configure authentication differently.
Set either the
FLIPT_STORAGE_OCI_AUTHENTICATION_TYPEenvironment variable or thestorage.oci.authentication.typeconfiguration property toaws-ecr. Additionally, make sure your compute instance or container has a role with permissions to pull from ECR.
Flag State Configuration
Each of Flipt’s filesystem backends expects you to represent your feature flag configuration via a set of YAML files. These files declaratively define what flags, segments, variants, etc. exist and in what configuration.Locating Flag State
Flipt’s filesystem backends allow you to define feature flags alongside other configurations in a shared directory, repository, or object storage bucket. Flipt uses a naming scheme to index which files are flag state files. By default, Flipt will look for the following filename patterns to attempt to parse as Flipt state:**/features.yaml**/features.yml**/*.features.yaml**/*.features.yml
features.yaml, features.yml, or with either extension .features.yaml or .features.yml is considered recursively from the root of your target.
If this naming convention doesn’t work for you, it can be overridden by creating a file named .flipt.yml in the root of your target directory tree. This file will be used to instruct Flipt on how to index your directory tree and find flag state files:
include and exclude. These can contain specific paths or glob-matching patterns.
The indexing process first matches the include section and then filters that are set by the exclude section.
Defining Flag State
Flipt flag state file format has been taken directly from Flipt’s existing import and export flag state format. You can runflipt export on your existing Flipt instance, and then
add/commit the result to a directory, object storage, or Git repository to get started.
This can be used to migrate from a relational database-backed instance of Flipt to a filesystem-backed deployment with ease.
features.yaml